
How to secure mission-critical work
The average data breach already costs organizations $4.45 million, and it appears that damages will only become more expensive as time goes on. In fact, one report found that cybercrime will cost the world $10.5 trillion by 2025.
While organizations can’t necessarily prevent hackers from targeting their systems, they can take proactive steps to strengthen cybersecurity and develop incident response plans that enable them to keep bad actors at bay and swiftly address incidents whenever they occur.
To help enterprises secure their mission-critical workflows and protect their most sensitive data, Anne Deming, head of enablement at Mattermost, recently hosted a webinar with Director of Security Daniel Schalla called Securing Mission-Critical Work: Overcoming Key Challenges to Effective Incident Response.
Keep reading for a brief overview of the webinar and a link to watch it in full on-demand.
No organization is immune from cyberattacks
Whether you work in healthcare, the public sector, financial services, or software, your organization relies on computer systems to generate revenue and deliver services. Whenever a breach occurs, the impacts are significant; organizations victimized by hackers can lose money, damage their reputation, and fail their customers. For example, if a healthcare company’s systems are inaccessible, the caliber of care can deteriorate.
As Miguel de Cervantes once wrote, being prepared is half the victory. By developing a robust incident response plan ahead of time, enterprises can position themselves to recover rapidly when time is of the essence.
“Companies need to prepare for incidents before they’re happening to enable efficient resolution,” Schalla says. “During an incident — which is a very hectic situation — is too late.”
Don’t have an incident response plan? Start somewhere
If your enterprise doesn’t have an incident response plan, you don’t have to reinvent the wheel. A number of incident response models exist, and you can follow them to start putting a plan in place.
For example, your incident response plan might have these four steps:
- Preparation
- Detection and analysis
- Containment, eradication, and recovery
- Post-incident activity
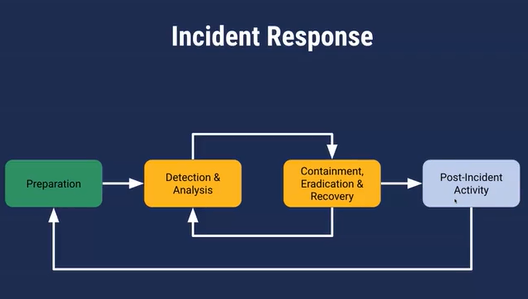
This is a broad framework — just a starting point. Plans will vary depending on what each environment looks like; a healthcare organization concerned about HIPAA-covered data will have different priorities than an enterprise seeking to comply with the GDPR, for example.
“If you don’t have a plan today, start with a very simple one,” Schalla explains, adding that your plan should cover which stakeholders to involve, where the incident response team will communicate, and what the high-level steps are.
In a world of ever-evolving requirements, it’s important to remember your plan should be fluid and adaptable.
“Incident response plans must change when your business and your requirements change,” Schalla says.
Use automation and integrations to increase focus
When an incident occurs, every second counts. This is why it’s so important to automate your incident response workflows as much as you can.
Using Mattermost Playbooks is one way to do that. With Playbooks, you can create checklist-based automations that ensure teams stay aligned during crisis scenarios. When an incident starts, you can click a button and automatically spin up a channel that brings relevant stakeholders together, with a pre-populated checklist of what needs to be done and who’s responsible.
“You bring structure in a very hectic process,” Schalla continues. “You have a lot of people responding to a very hectic event and can make sure everyone follows the same process.”
Similarly, ideal incident response tooling should also integrate with the security tools your team uses. As an example, Schalla presents a scenario of a 10-person incident response team, each of whom needs to toggle between several tools to find information.
“Imagine everyone switching tools and needing to authenticate,” he says. “It’s a lot of work to pull information back, and then everyone needs to do it.”
With a flexible incident response solution in place, teams can connect it to the other tools they need to resolve incidents and automatically pipe relevant information into the appropriate channels.
“It’s saving your team time and allows you to limit the damage by being more effective in your response,” Schalla says.
Is your mission-critical work secure?
To learn more about how to secure mission-critical work — and how Mattermost can help you streamline incident response and accelerate mean time to resolution — watch the webinar in full.




