Advanced access controls with Mattermost Enterprise Edition
While some smaller companies may only need to use standard access controls to shore up systems, large organizations — particularly those with strict security, confidentiality, and compliance requirements — often require advanced functionality that gives them more authority over which users can access what systems and when.
In this piece, we examine some of the main reasons why enterprise organizations need robust access controls — and how Mattermost Enterprise Edition delivers on that promise.
Why do enterprises require advanced access controls?
Enterprise organizations require software that includes advanced access controls for a variety of reasons. We’ll examine some of the most persuasive ones in this section.
Information security
Large enterprises typically handle sensitive, mission-critical data. Advanced access controls help ensure that bad actors can’t access the most important information a company possess — like intellectual property, trade secrets, financial data, and personally identifiable information (PII). As a result, enterprises can protect themselves against exorbitantly expensive data breaches and leaks, maintaining their competitive edge.
Compliance
Many industries need to follow strict regulations governing data privacy and security, including GDPR, CCPA, HIPAA, and PCI DSS. Violating such regulations can result in significant monetary and reputational damage. By implementing advanced access controls, organizations can maintain compliance with these regulations, avoiding costly fines, legal repercussions, and reputational harm.
Productivity
Advanced access controls enable administrators to ensure that employees have access to the data and tooling they need to do their jobs — no more, no less. As a result, they’re less likely to be overwhelmed by too much information, since they’ll only be able to access what they need. At the same time, this also reduces the chances an employee inadvertently mishandles or corrupts data that they don’t need. Taken together, these benefits enhance overall team productivity.
Audit trails
To maintain compliance and know which users accessed what data and when, enterprises often look for software solutions that automatically create audit logs. In the event a security incident occurs, administrators can easily tell which users are responsible. At the same time, audit trails also help organizations keep track of who made what changes and demonstrate compliance during audits.
Risk management
Access controls help enterprises manage both internal and external threats effectively. Not only can advanced controls prevent insiders from sabotaging the organization by ensuring only authorized individuals can access key data, they also make it much harder for outsiders to breach systems and steal information. Taken together, this strengthens the organization’s risk management posture, decreasing the chances internal or external bad actors target them.
Incident response
For large enterprises, it’s not a question of whether an incident will happen but when. When incidents strike, advanced access controls help the team respond more swiftly, ensuring that only authorized users can access critical systems. At the same time, admins can use advanced controls to rapidly revoke access to impacted systems, isolate them, and contain the breach. Add it all up, and robust access controls can help minimize disruptions, data theft, and remediation costs — helping organizations substantially mitigate the impact of incidents.
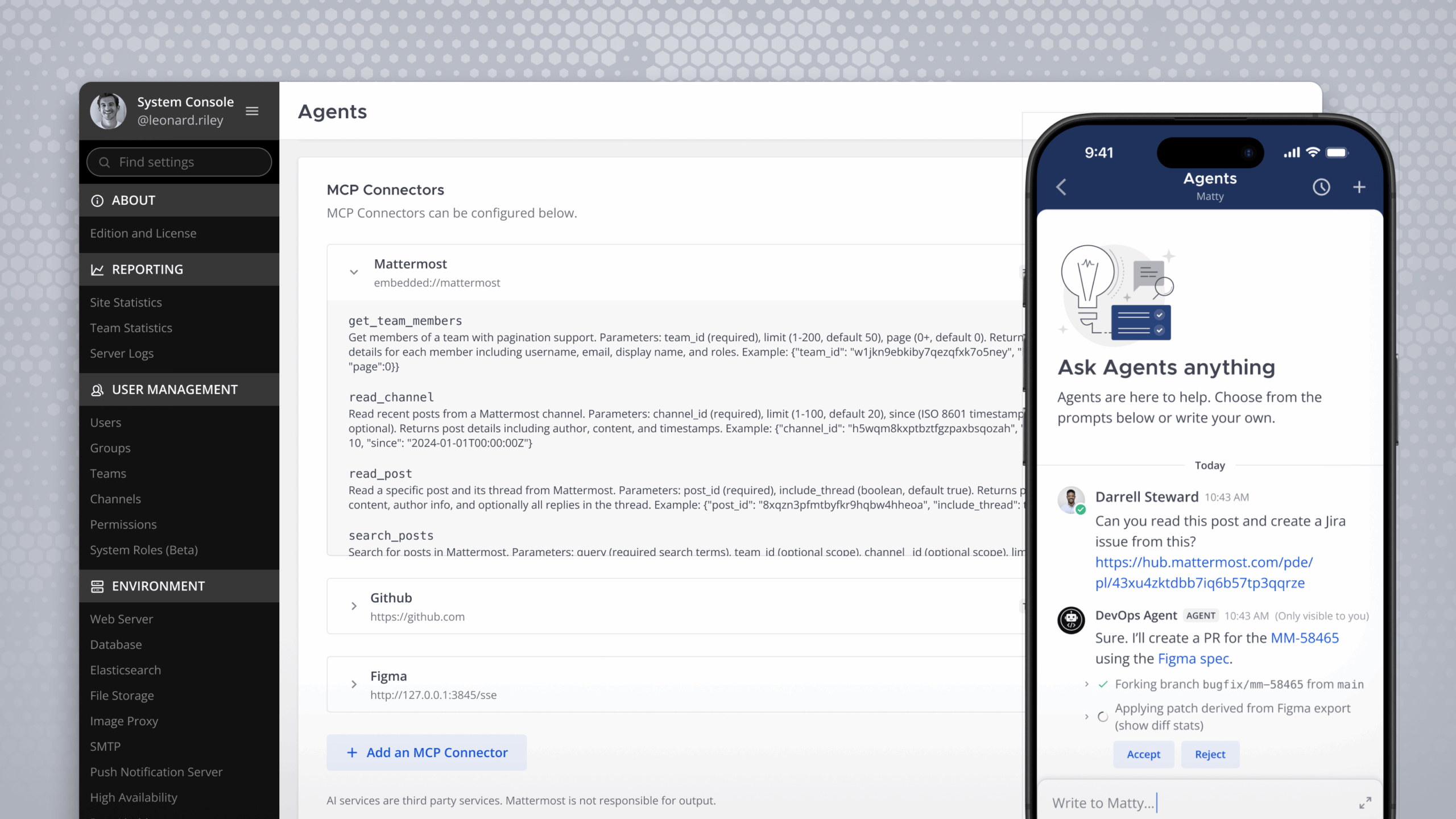
Mattermost Enterprise Edition: Advanced access controls
As a secure collaboration hub purpose-built for technical and operations teams working in complex environments with the highest requirements, Mattermost Enterprise Edition delivers several types of access control configurations designed to help organizations fortify network and information security and keep systems protected. These features are split across two categories:
- User provisioning and authentication
- Granular permissions
1. User provisioning and authentication
To protect networks and applications, system administrators must be able to provision users rapidly and be able to verify the identity of each user trying to access systems and data.
AD/LDAP user and group sync
AD/LDAP user and group sync is a process in which an organization’s user accounts and group memberships are synchronized between different systems to ensure consistent access controls and authentication across various applications and services.
When Enterprise Edition customers integrate their AD/LDAP system with Mattermost, users can access the secure collaboration hub without having to create new credentials. Administrators are also able to automatically assign users to groups (e.g., “pmteam” and “marketing”) for faster, more secure account provisioning.
Single sign-on (SSO)
In addition to strengthening the user experience, helping employees save time by logging in with a single button, and improving team productivity, SSO also improves enterprise security, particularly when coupled with multi-factor authentication (MFA), by reducing the likelihood a bad actor is able to access an employee’s account. For example, by eliminating the need for employees to enter their login credentials throughout the day, users are much less likely to fall victim to phishing attacks and enter their usernames and password on malicious websites.
Mattermost Enterprise Edition supports both MFA and SSO, via Google, GitLab, OpenID Connect, Office 365, or by synchronizing SAML with Okta or OneLogin. As a result, system administrators can easily see which users access what systems and can detect unusual and suspicious login patterns at a glance.
Granular permissions
Enterprises require more than general permissions. They need granular permissions, or fine-grained controls that enable them to configure what actions and operations users can perform inside software systems.
Mattermost Enterprise Edition includes role-based access control that enable admins to configure and enforce granular permissions at a highly detailed and specific level.
What is role-based access control?
Role-based access control (RBAC) is an architectural approach to security that restricts system access and permissions based on users’ role within an organization. In RBAC, access is associated with roles, and individuals are assigned to specific roles based on their job functions.
This approach simplifies access management, making it easier to grant or revoke permissions as users change roles. At the same time, RBAC enhances security by ensuring that users can only access the resources necessary to do their jobs.
Advanced team permissions
Enterprise Edition admins can determine which users can perform certain actions — like creating teams, managing channels, and configuring webhooks. Using Team Override Schemes, system administrators can customize permissions for each team, enabling them to collaborate in a unique way. Learn more about advanced permissions in Mattermost Enterprise Edition.
Custom admin roles
Admins can also create custom system admin roles in Enterprise Edition, including system manager, user manager, custom group manager, and viewer. These roles govern what areas of the System Console users can access. Learn more about custom admin roles in Mattermost Enterprise Edition.
Custom user groups
Custom groups improve focus by ensuring only authorized users get notified in specific channels while maintaining transparency for other stakeholders. By creating a custom user group — e.g., product, finance, and HRteam — users associated with that group will receive notifications the same way they’d be alerted if you @mentioned them directly. Learn more about managing custom groups in Mattermost Enterprise Edition.
Learn more about Mattermost Enterprise Edition
Mattermost Enterprise Edition includes powerful access controls for enterprises. But the benefits of the premium solution don’t stop there.
To learn more about what’s inside Mattermost Enterprise Edition, check this out.