Join the alpha program for Mattermost’s new Incident Response Workflow app
Note: Mattermost Incident Response Workflow (DevOps Command Center) is in closed beta until further notice.
Is your InfoSec or DevSecOps team ready to resolve issues as quickly as possible?
To help accelerate response times, we’re happy to announce the alpha release of the Mattermost Incident Response Workflow application for Enterprise Edition, supported in Mattermost 5.12 and later.
The app is designed specifically for incident response and enables you to connect all your workflows, automate repetitive tasks, and collaborate on incidents—all without leaving Mattermost.
Though it’s still in its early stages, the app is already significantly more powerful than many other workflow builders on the market. With the Mattermost Incident Response Workflow application, your team can:
- Reduce duration of outages and security exposures by decreasing resolution time via automated incident response workflows
- Decrease cost of servicing incidents by automating common and routine responder tasks
- Assess and forecast threats by quickly searching and navigating incident history
The need for faster incident response
Unplanned downtime and security breaches are both prohibitively expensive. When your systems go down unexpectedly or a malicious actor infiltrates your network, you need to take immediate steps to resolve the situation. It’s that simple.
Otherwise, productivity grinds to a halt and the user experience crumbles until your network and apps are brought back online. On the other hand, depending on how bad your breach is and whether any privacy laws were violated (e.g., HIPAA and GDPR), you may incur hefty penalties.
Suffice it to say that organizations need to be able to quickly address unplanned downtime and respond to breaches rapidly.
Yet one recent IBM study found that 77 percent of organizations lack a formal incident response plan. And despite all of the reporting on the costs associated with unplanned downtime and data breaches in recent years, 57 percent of companies indicate that it’s taking more time to respond to cybersecurity incidents than before.
The Mattermost Incident Response Workflow app solves these problems by automatically bringing the right people, tools, files, and bots together in one place, enabling your team to respond to critical issues right away.
The Incident Response app in action
To give you a better idea as to how the app helps your team to respond to issues faster, look at this example:
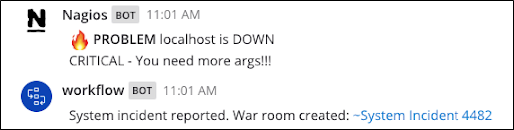
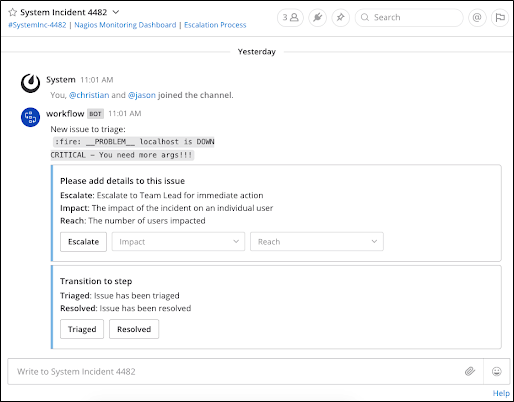
Here’s how the app works in the hypothetical incident illustrated above:
- An incident is detected in a monitoring system and posted to a Mattermost channel.
- Automated incident response workflows are triggered based on relevant keywords (e.g., #security-critical).
- InfoSec and DevSecOps teams are automatically notified when an incident occurs via email, mobile push, and desktop notifications.
- A war room channel is created automatically; InfoSec and DevSecOps teams are immediately invited to begin collaborating on the critical incident.
- A message posts to the war room channel containing relevant information in one place, including incident data, links, and quick actions to take.
- Once the incident is resolved, the war room channel is archived to declutter your channel sidebar while preserving the information for future use.
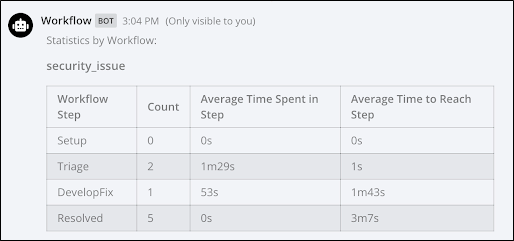
As an added bonus, admins can also pull automated incident response statistics with a single slash command, including mean time to acknowledgment (MTTA) and mean time to resolution (MTTR).
Getting started
If you’re interested in trying the Mattermost Incident Response Workflow app, here’s how you can get started:
- Sign up for the closed alpha program. If you’re selected to join the program, we’ll send you an email with a plugin binary.
- Upload the plugin binary in System Console > Plugins > Plugin Management following these steps.
- Enable the plugin on the Installed Plugins list.
- Use one of these sample app workflows to try the app. For instructions on how to do that, go here.
- Post the trigger word defined in the workflow schema to start the workflow.